Open banking api traffic is projected to jump from 137 billion calls in 2025 to 722 billion by 2029, with users rising from 183 million to over 645 million in the same period, according to Juniper Research’s open banking API market outlook. For developers, that changes the conversation. Open banking isn’t a niche fintech feature anymore. It’s becoming infrastructure.
If you build eCommerce SaaS, that should sound familiar. You already deal with fragmented platforms, permissioned access, brittle schemas, version drift, and customer expectations for near real-time sync. Open banking api development has the same shape, just with stricter security and regulation. Banks are standardizing access to accounts, balances, transactions, and payments in the same way commerce platforms have spent years trying, and often failing, to standardize access to orders, products, customers, and inventory.
That parallel matters. Once you see open banking as a model for secure, permissioned, multi-provider integration, the practical lessons become useful far beyond finance.
The Unstoppable Rise of Open Banking APIs
A 427% jump in API traffic over four years changes how teams design products. As noted earlier, open banking usage is scaling fast enough that API reliability, consent handling, and schema consistency are no longer background concerns. They shape the product experience.
For developers, that shift should feel familiar. Open banking turns fragmented bank connectivity into a managed interface problem, much like multi-store commerce turns Shopify, Magento, WooCommerce, BigCommerce, and marketplaces into an integration layer you have to normalize and support over time.
An open banking api gives third-party apps a controlled way to read financial data or initiate payments after the user approves a defined scope. The practical win is simple. Your product no longer needs to ask for banking credentials or depend on brittle workarounds. It can request access through supported flows, receive structured data, and operate within rules that are explicit enough to audit.
That model matters well beyond FinTech.
If you build ERP, OMS, reconciliation, analytics, or subscription software for merchants, the pattern is the same. Users expect one product surface, even when dozens of providers sit behind it. They expect stable sync, predictable field mapping, and permission models that do not create extra support tickets.
Three implications show up fast:
- Connector count changes the job: One bank or one commerce platform is an integration project. Twenty becomes an API product.
- Permission design affects adoption: Broad access requests slow onboarding. Tight scopes improve trust, but they can force more reauthorization flows later.
- Normalization is where delivery time goes: Raw provider coverage looks good in a roadmap. Consistent behavior across providers is what your customers pay for.
I have seen teams underestimate the third point. Shipping the first connector feels fast. Proving six months later that the endpoint is still necessary, monitored, documented, and compliant is the core discipline.
That is why docs and change management carry so much weight. Technical Documentation Best Practices applies here because unclear contracts create the same failure mode in banking and eCommerce. Different teams interpret edge cases differently, support inherits the ambiguity, and production becomes the source of truth.
Open banking also points to a broader product direction. The winners are usually the companies that hide provider fragmentation behind one dependable interface. That is the same reason unified commerce layers matter. If your SaaS needs one connection to many stores instead of custom work for every platform, the broader future of APIs in digital products looks a lot like what API2Cart solves for eCommerce.
Understanding Core Concepts and Regulations
An open banking api is easiest to understand as a universal adapter for financial data, but with legal and security rules attached. Your application doesn’t scrape a bank website or store a customer’s banking password. Instead, it asks for a defined permission, the bank authenticates the user, and the bank returns only the data or action scope the user approved.
The two roles developers should know
In product discussions, two categories show up constantly.
| Role | What it does | eCommerce analogy |
|---|---|---|
| AISP | Accesses account and transaction information with user consent | Analytics or reporting app pulling order history |
| PISP | Initiates payments on the user’s behalf with consent | Checkout service triggering a payment action |
That distinction matters because read access and write access create different risk profiles, different UX patterns, and different operational burden. Teams often underestimate this. Reading transaction history feels like “just another API.” Initiating a payment is closer to running checkout in a regulated system.
Why regulation shaped the ecosystem
The modern market took off because regulation forced standardization. The global open banking movement accelerated through the EU’s PSD2 in 2018 and the UK’s CMA Open Banking Order in 2017 to 2018, which compelled major banks to develop standardized APIs according to Ozone API’s history of open banking.
For developers, PSD2 and the UK framework changed three things:
- Banks had to expose APIs: Integration stopped being optional or purely partner-driven.
- Third-party access became formalized: Authorized providers got a regulated path to build products.
- Security got stricter: Authentication and consent became built-in parts of the flow.
The UK implementation is especially relevant because it pushed common standards across major banks instead of leaving every provider to invent its own version. That’s similar to what every commerce SaaS team wants from cart and marketplace ecosystems but rarely gets cleanly.
If you’ve ever mapped ten “customer” objects from ten commerce platforms into one internal model, you already understand why regulated standardization can speed up product development.
The regulatory direction in the US has been more fragmented, which is why market watchers keep an eye on policy developments like New York's Open Banking Bill. Even if you don’t build for banks directly, regulation tells you how stable or fragmented the next integration wave will be.
How Open Banking Authorization Actually Works
The core open banking api flow is a three-party interaction between the user, your app, and the bank. Most confusion comes from treating it like a normal API key integration. It isn’t. The bank is the authority, the user is the approver, and your app is a delegated client.
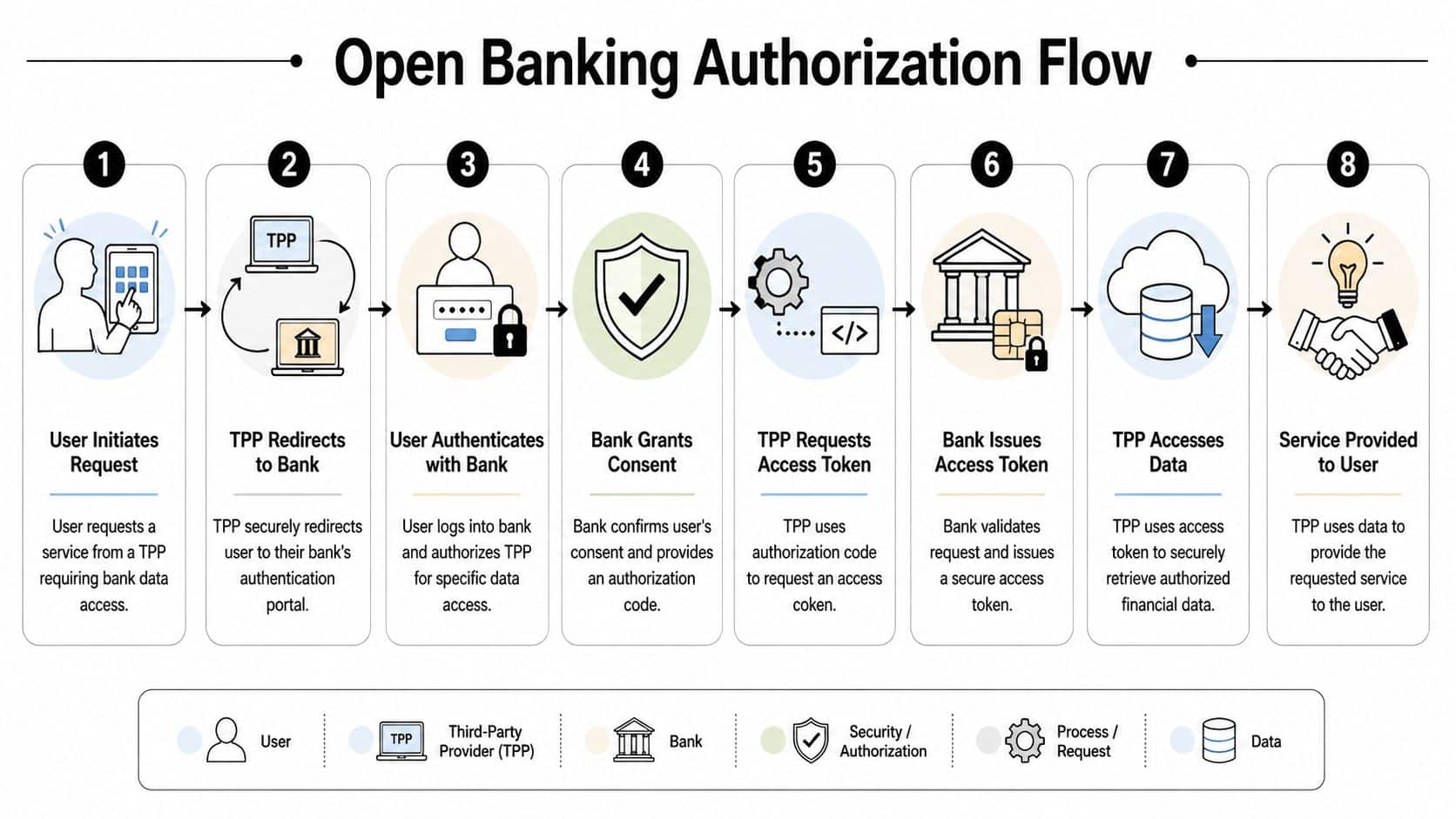
The flow in plain developer language
A typical authorization sequence looks like this:
- Your app starts a request when the user wants a feature that needs bank data or payment access.
- Your app redirects the user to the bank rather than collecting banking credentials itself.
- The user authenticates with the bank and reviews the requested permission scope.
- The bank records consent and returns an authorization artifact to your app.
- Your backend exchanges that artifact for a token through the bank’s authorization server.
- Your app calls the bank API with the token to fetch approved data or initiate an allowed action.
- Your product turns that data into a user-facing workflow such as verification, reconciliation, or payment.
For eCommerce developers, the closest analogy is OAuth app installation for a commerce platform, except the security and consent language are tighter and the failure handling matters more.
What standards sit underneath
The standards stack is broader than a few REST endpoints. Open Banking API specifications include Read/Write APIs, Open Data APIs, and Directory Specifications for managing Third-Party Provider registration, and this standardized approach reduces integration complexity as described in the Open Banking API specification framework.
That means a production integration usually has to think about more than request and response payloads:
- Read/Write APIs: The business endpoints your product uses.
- Open Data APIs: Public information that supports discovery and presentation.
- Directory mechanics: How trusted participants are identified and managed.
- Client registration workflows: How the app becomes a known client in the ecosystem.
- Monitoring expectations: How operational reporting gets standardized.
This is one reason open banking implementations often fail when teams assign them to “the API engineer” as a side task. The job spans identity, consent UX, app registration, token lifecycle, and domain modeling.
The first version usually breaks at the consent boundary, not at the JSON boundary.
Token handling is where teams get sloppy
OAuth 2.0 drives the authorization pattern. In practice, you’ll deal with short-lived access tokens, consent scopes, and in many cases refresh behavior that has its own rules. Don’t reduce this to “we have a bearer token now.”
A few implementation habits help:
- Store only what you need: Keep token data and consent metadata minimal and traceable.
- Model permissions explicitly: “Read balances” and “initiate payment” should never collapse into one generic access flag.
- Design for expiry: Token expiration is a normal state, not an edge case.
- Separate user identity from bank connection state: It makes retries, reconnect flows, and support debugging much cleaner.
If your team works across commerce integrations too, comparing OAuth vs JWT in integration security models can help clarify where delegated authorization ends and token format discussions begin. Teams often mix those concepts together and make bad architectural calls because of it.
Key Data Endpoints and Common Schemas
Once authorization works, developers stop talking about consent screens and start talking about payloads. That’s where an open banking api becomes either useful or frustrating. The category names are straightforward. The challenge is building a domain model that survives provider variation.
Accounts and balances
The simplest implementation usually starts with account discovery. Your app asks the bank what accounts the user has shared, then fetches balance information for the selected ones.
A typical internal normalized object might include:
- Account identifiers: Your own connection IDs plus whatever provider account reference is safe to store
- Display fields: Account nickname, masked number, type
- Currency and status: Enough to render the account correctly in product flows
- Available and current balance values: Kept separate because product logic often depends on the distinction
For an onboarding or verification workflow, this can be enough. A lender might check account existence and consistency. A treasury tool might use the same data to let a finance team choose the funding account for a payment run.
Transactions
Transactions are where product ideas multiply. One feed can support reconciliation, cash flow visibility, underwriting inputs, and spend analysis. But transaction schemas also expose the usual integration pain: provider-specific descriptions, inconsistent merchant naming, pending versus booked states, and category fields that don’t line up.
A normalized transaction model usually needs these concepts:
| Data group | Why it matters |
|---|---|
| Amount and currency | Core financial logic, summaries, anomaly checks |
| Booking and value dates | Reporting and settlement timing |
| Description fields | Human-readable audit trail |
| Counterparty or merchant detail | Matching and categorization workflows |
| Status | Distinguishing pending from completed activity |
A finance SaaS product might ingest transactions to match payouts against orders. An accounting tool might enrich descriptions and route them into rules. A budgeting app might layer category logic on top. The raw endpoint is just the start.
Payments
Payment initiation endpoints move the integration from passive visibility to active workflow. That’s where teams need stronger operational controls. The schema usually includes debtor and creditor context, amount, currency, references, and execution state, but the bigger concern is idempotency, user messaging, and error recovery.
If you’ve built commerce checkout or payout systems, the pattern is familiar. You don’t just need a successful request. You need a stable state machine around “created,” “pending,” “accepted,” “failed,” and “requires user action.”
Good integrations don’t just fetch financial data. They turn inconsistent provider payloads into a reliable product state your support team can explain.
Real-World Use Cases for SaaS and eCommerce
The fastest way to understand open banking api value is to map it to workflows you already build in SaaS and commerce. Not abstract fintech demos. Actual product jobs.
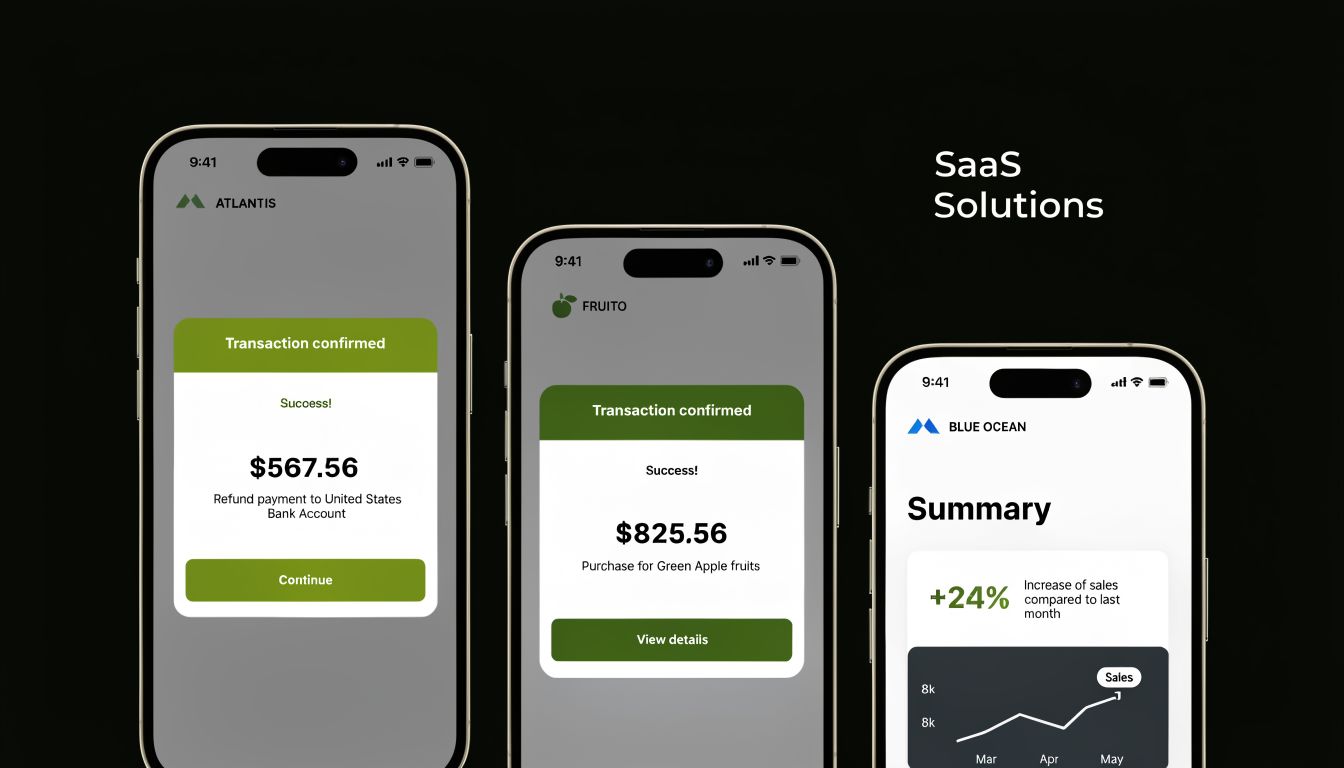
Four practical patterns
Account verification during onboarding
If your product needs to confirm that a user controls a bank account, open banking gives you a cleaner path than document upload or manual bank proof. That shortens the route from signup to usable account state. For marketplace platforms, lending products, and seller tools, that’s a direct product win.
Pay by bank at checkout
Some merchants want a bank-based payment option instead of adding yet another card flow. Payment initiation APIs can support that pattern. The hard part isn’t only payment creation. It’s consent UX, failure messaging, and reconciliation after the payment event lands.
Financial reconciliation for merchants and platforms
The commerce analogy is particularly apt. Orders live in one system, settlements in another, payouts in another, and the bank account confirms what funds moved. Open banking data helps close the loop.
Cash flow and expense intelligence
Transaction feeds can support finance automation features that merchants use. A good example of the product direction is automatic expense categorization, where raw financial data becomes something operationally useful instead of just another ledger export.
The parallel eCommerce developers should notice
Open banking solved a problem commerce developers know too well. Too many providers. Too many schemas. Too many “almost standard” APIs. The answer in banking has been to push toward secure, permissioned, standardized access.
That’s the same integration logic behind unified eCommerce access. Instead of building one connector for Shopify, another for Magento, another for WooCommerce, another for Amazon, and then maintaining all of them forever, teams want one abstraction layer for orders, products, customers, inventory, and shipments.
Here’s the practical lesson: the product value rarely comes from the connector itself. It comes from what your app does once the connector is dependable.
- OMS platforms care about order import and fulfillment coordination.
- PIM tools care about catalog sync and listing consistency.
- Shipping software cares about shipment creation, tracking updates, and status feedback loops.
- Analytics products care about normalized events they can trust.
What works and what doesn’t
What works is building around stable user jobs. Verify account. Reconcile payout. Initiate payment. Sync inventory. Import orders.
What doesn’t work is exposing raw provider complexity directly to customers and pretending the integration layer is done.
Teams ship faster when they normalize capabilities, not just endpoints.
That principle applies equally to bank APIs and commerce APIs. The winning products hide source-system chaos behind dependable workflows.
Implementation Best Practices and Pitfalls
Production failures in open banking usually come from everything around the API, not the endpoint itself. The happy-path demo works. Trouble starts later, when consents expire, refresh tokens fail, one bank interprets a spec differently, and support needs to explain why data stopped syncing for a specific merchant account.
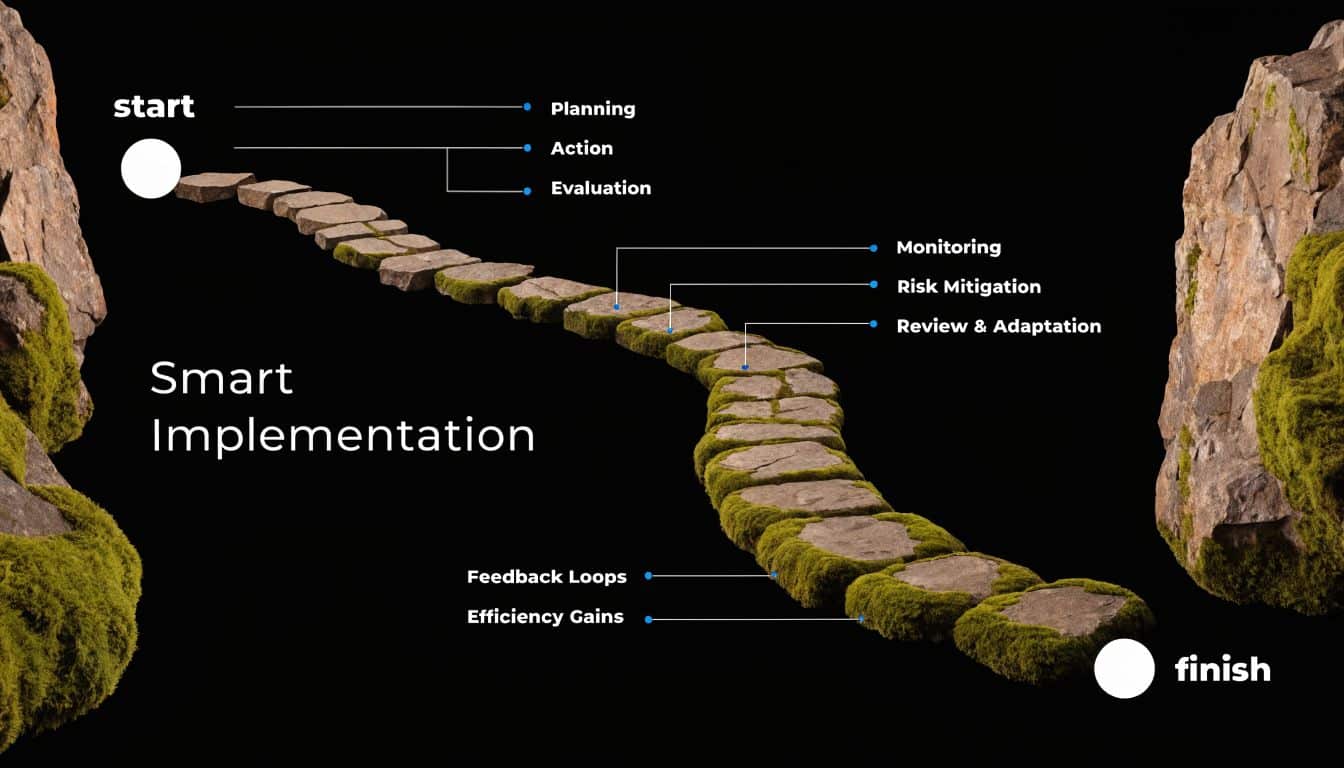
Start with the security baseline
Open banking integrations sit on OAuth 2.0, and many implementations add mutual TLS and FAPI controls to tighten client authentication, request integrity, and consent handling. For a product team, that means security decisions cannot live only in app code. They need to show up in infrastructure, key management, logging, and support workflows.
A few rules hold up well in production:
- Request the smallest scope set possible: Extra permissions increase review burden and user distrust.
- Treat mTLS and certificate rotation as platform operations: If renewals are manual, they eventually fail at the worst time.
- Store a clear consent timeline: Your team should be able to answer who approved access, for what, and when it changed.
- Keep secrets out of business logic: Application services should call a secure credential layer, not handle raw secrets directly.
Teams building connector-heavy SaaS products run into the same classes of problems in commerce APIs. These API security best practices for integration-heavy platforms map well because the attack surface is similar: external auth flows, shared infrastructure, sensitive data movement, and long-lived integrations.
Put control points in the right place
An API gateway will not fix a weak integration design, but it does reduce repeated work and policy drift. That matters once multiple services consume bank data or initiate payments.
The gateway is usually the best place to centralize a few things:
| Concern | Why it matters in production |
|---|---|
| Token validation | Keeps authorization behavior consistent across services |
| Rate limiting and traffic shaping | Stops one client, bank, or retry storm from degrading the whole platform |
| Request and response transformation | Helps absorb provider differences without spreading mapping logic everywhere |
| Policy enforcement | Gives security and compliance teams a single control point |
eCommerce developers will recognize the pattern. If you have ever hidden Shopify, Magento, WooCommerce, and marketplace quirks behind one normalized API, the same logic applies here. Open banking needs a disciplined abstraction layer. Unified commerce access needs one too, which is why platforms like API2Cart reduce connector sprawl before it reaches product code.
Watch for shadow APIs and connector drift
The hard bugs often come from endpoints nobody planned to keep. A temporary callback handler stays live. A partner-specific route bypasses normal policy checks. A migration endpoint keeps access to data it no longer needs. In finance, that creates audit and security risk. In eCommerce, it creates brittle sync behavior and expensive support cases.
Control starts with ownership. Every endpoint that touches financial or commerce data should have a named owner, a reason to exist, and a retirement plan.
A practical checklist looks like this:
- Maintain an API inventory: Include internal tools, partner-facing endpoints, and deprecated routes.
- Review provider changes centrally: Scope changes, payload drift, and auth updates should not surprise downstream teams.
- Log lifecycle events, not just request errors: Consent granted, consent revoked, token refreshed, token refresh failed, account relinked.
- Design recovery paths into the UX: Users need a clear next action when access expires or a provider returns partial data.
Shipping another endpoint is easy. The core discipline is proving six months later that the integration still has a valid purpose, monitoring, and compliance coverage.
Teams that handle this well treat integration architecture as a product capability with ongoing maintenance cost. Teams that ignore that cost usually end up rebuilding auth flows, patching one-off connectors, and explaining inconsistent data to customers.
Developer Resources and Your Next Steps
If you want to get hands-on with open banking api development, start with standards and sandbox thinking before you write production code. Read the UK Open Banking specification set, inspect bank developer portals, and test how your app handles redirected consent, token renewal, and partial failure states. Those exercises expose design flaws quickly.
A practical learning path looks like this:
- Read the specification models closely: Focus on Read/Write APIs, directory concepts, and client registration.
- Prototype your internal normalized schema early: Don’t wait until the third provider to define account, balance, transaction, and payment models.
- Build failure-first UX: Expired consent, revoked access, and bank-side auth interruption should all have clear user messaging.
- Create observability from day one: Log consent state changes, token events, and provider-specific response anomalies.
- Apply the same lessons to commerce integrations: Permissioning, normalization, and connector lifecycle discipline transfer directly.
The broader takeaway is simple. Modern SaaS products win when they turn fragmented external systems into one coherent developer and user experience. Open banking made that explicit in finance. The same engineering logic applies across eCommerce.
If your team needs that same unified approach for commerce data, API2Cart gives B2B software vendors a single API for connecting with 60+ shopping carts and marketplaces. Instead of building and maintaining one-off integrations to Shopify, Magento, WooCommerce, Amazon, eBay, Walmart, and others, you can use one integration layer to work with orders, products, customers, inventory, shipments, and catalog data. It’s a practical way to speed up delivery, reduce connector maintenance, and validate multi-platform workflows faster.